Internet security has been hotly debated in recent years. Users began to give more importance to the topic as they began to understand more about the importance of their data. In addition, it is also essential for companies to adopt protection tools to avoid the challenges that a data leak can generate – and how valuable information is for their business. In addition, of course, we are also experiencing an exponential increase in cyber attacks.
Data from the latest Microsoft Digital Defense Report, published in November 2022, show that, in 2021, around 921 password attacks were recorded per second, an increase of 74% compared to the previous edition of the survey. The most common attacks are ransomware (data hijacking), which in addition to duplicating and blocking data, directly affect sectors such as Industry (28%), Health sector (20%), Retail (16%), Education (8% ), Energy (8%), Finance (8%), Governments (8%) and IT (4%).
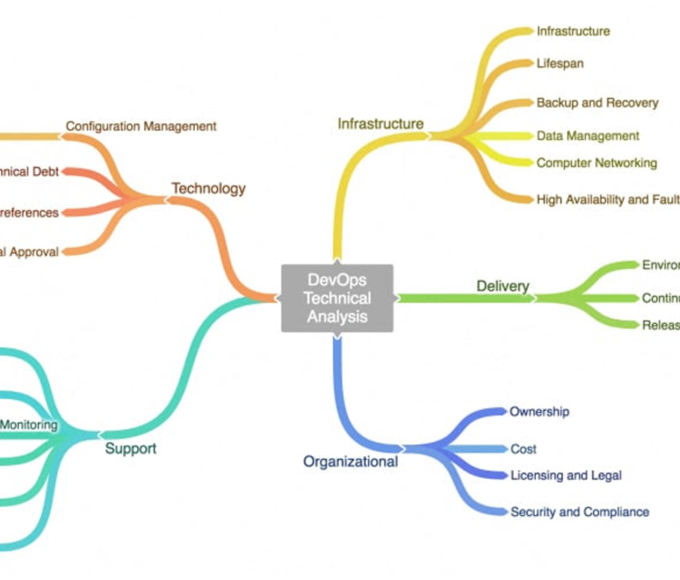
And the theme also affects the work of developers, and the lack of security policies for those who work with the development of codes and applications can also be one of the gateways for cyberattacks. However, it is worth mentioning that several tools are currently available that were developed to help these professionals to work following the best cybersecurity practices. The Security Development Lifecycle (SDL), which in free translation means security development lifecycle, is an example.
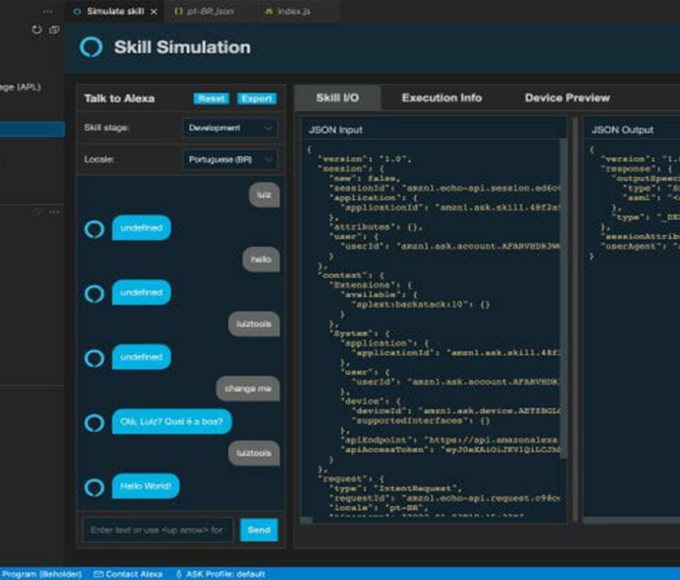
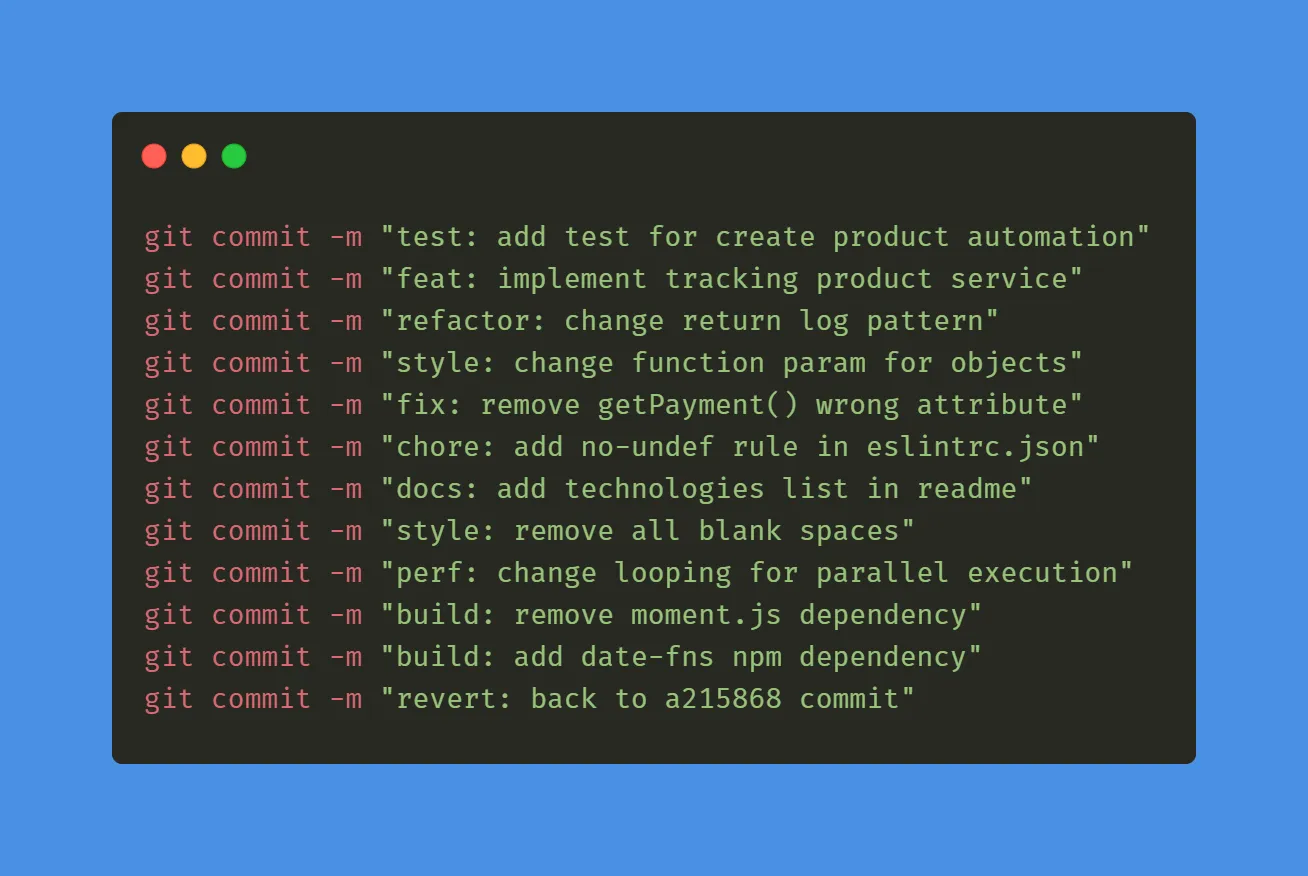
It consists of having clear policies that include, among other things, access to tools based on Software as a Service (SaaS) and code repositories (through SSH, HTTPS, or personal access token). For access to the SaaS-based environment, it is important to give visibility to the instructions on how the access principles determine who can download (clone) code repositories from systems and on which servers (local, cloud, and container).
But as we know, developers often work with their machines – which means even greater care is taken to protect those devices. The situation can be more delicate if they use a remote connection with vulnerable Wi-Fi networks, where the risk of theft, loss of hardware, and encryption become major concerns. Therefore, it is also essential to monitor and apply security in these networks.
IT teams need to be able to have these controls in place, as malicious extensions can endanger developer tools and cause company-wide breaches. Therefore, some tools can support technology teams and professionals working with development, such as GitHub Advanced Security and Defender for DevOps, embedded in Microsoft Defender Cloud. Both tools help reduce the number and severity of vulnerabilities, helping professionals and organizations integrate security into every step of the development cycle. Likewise, Defender for DevOps also brings this possibility and, best of all, in multi-cloud environments, which are increasingly common in companies. It is also important to pay attention to the professionals’ access to the company’s network. For example, OneDrive can block or limit unmanaged device access. They are tools available to make life easier for programmers and bring security.
GitHub also has some tools to mitigate any vulnerabilities by automatically applying controls from the developer environment in the cloud, in addition to indicating zero trust measures, such as minimum privilege settings with limits on who can change and approve the code.
Another advantage is the possibility of a unified visibility of security for professional developers, from the construction of the code, through the pre-production of the application, including vulnerability scans in open source or not, regardless of where this information is, and in one or more cloud platforms.
In addition to all preventive actions, training to enable teams to manage security, with practical examples of how to protect applications and resources from code to the cloud, are available on platforms such as Microsoft Learn, and is necessary. With the knowledge of the importance of security throughout the code and application development cycle, it will certainly be easier to identify, right at the beginning, critical problems that may arise, mitigating possible cyber-attacks.
*O conteúdo deste artigo é de responsabilidade do(a) autor(a) e não reflete necessariamente a opinião do iMasters.




















Leave a comment